Every day, cybercriminals scan the web for vulnerabilities to bypass and collect data from organisations and use it for malicious intentions. According to a study published by Statista, 18,325 security vulnerabilities were identified in 2020, the highest number reported to date. Such alarming figures are why companies cannot afford to delay conducting a vulnerability assessment of their organisations IT infrastructure.
An IT vulnerability assessment helps you to identify security gaps that attackers would likely exploit and develop strategies to fix these security loopholes. Besides identifying loopholes, an internet vulnerability assessment helps develop proactive security management programs that quickly identify and neutralize threats.
Below is an analysis of what a vulnerability assessment entails and a step-by-step guide to developing one.
What Is Vulnerability Assessment?
A vulnerability assessment is a systematic audit of your IT environment to identify, test, classify, and prioritize security weaknesses. The assessment reviews your system’s vulnerabilities and recommends mitigation solutions to resolve the gaps identified.
A vulnerability can either be a software design flaw that’s easily exploited or a gap in the company’s security program, which an attacker can also manipulate.
Moreover, a vulnerability assessment is a great tool to identify and prevent commonly known threats such as:
- Remote Code Execution (RCE) attacks – this form of attack is also known as code injection attacks. A vulnerability scan can also identify SQL injections and Cross-Site Scripting (XSS) attack vectors.
- Insecure software defaults – Insecure default settings expose devices such as routers to attackers who can easily access credentials and hack into your company’s system.
- Unpatched security vulnerabilities
- Hidden backdoor software programs
- Uncontrolled superuser account privileges
- Automated script execution without malware checks

Vulnerability assessments can either be manual or automated, depending on the degree of testing and coverage required. Additionally, assessments target different technology categories, with the most common levels being application-layer and network-based reviews.
Purpose of Vulnerability Assessment
The primary purpose of vulnerability assessment is to test and identify security gaps within a company’s network and then use the findings to create recommendations, policies, and procedures to resolve the loopholes identified. In addition, these are the common objectives of vulnerability assessments:
- During the assessment process, the team takes stock of the company’s security programs and highlights the weaknesses present. From there, they perform tests to identify your system’s likelihood of being breached by attackers.
- The vulnerability assessment team also establishes how many potential attacks can compromise your IT environment during a successful breach.
- IT administrators get accurate inventories of all their IT equipment. The process starts with identifying flaws. To do this successfully, you need a proper inventory of all your company’s IT assets.
- To test and discover vulnerabilities within your IT environment. Exposures can range from incorrect configurations to critical system design shortcomings.
- To document the security weaknesses identified for developers to reproduce the discoveries.
- To create guidelines to develop remediation solutions with the vulnerabilities identified.
- A vulnerability assessment helps in understanding the security return on investment. Organizations can easily justify their future security expenditure by seeing where security resources go into protecting the company.
- Lastly, the purpose of a vulnerability assessment is to equip organizations with tools to handle potential future attacks and to resolve successful attacks before they affect the whole organization quickly.
Vulnerability Assessment Working
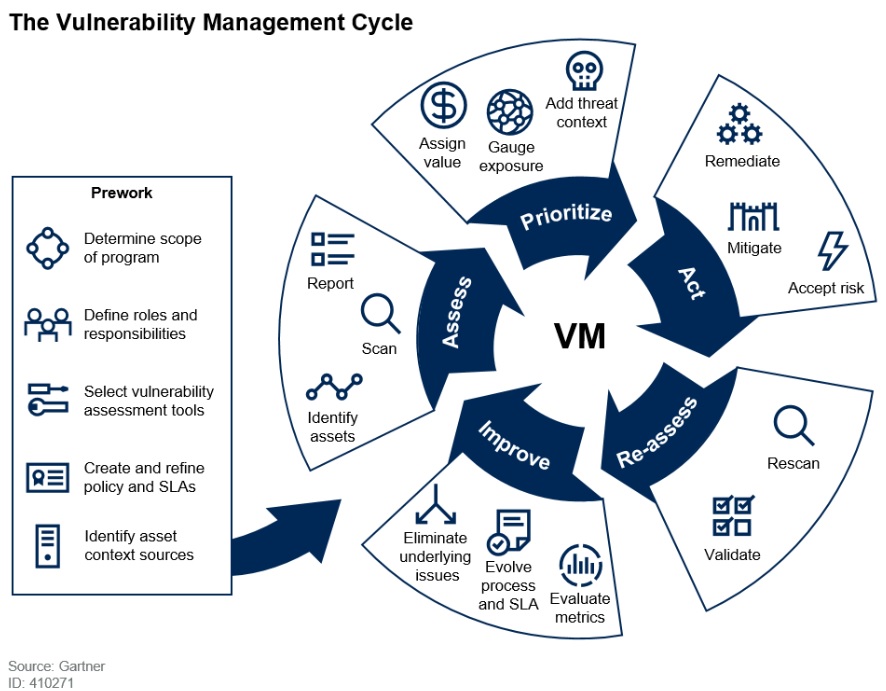
The vulnerability assessment objectives identified above help develop a vulnerability assessment scope of work, including vulnerability testing methodologies, tools, and a step-by-step implementation plan.
It’s vital to understand how a vulnerability assessment works by looking at various testing approaches. These vulnerability testing methods adopt automated or manual scanning techniques to identify flaws within a company’s IT environment.
One such method is Static Application Security Testing (SAST), also known as static analysis or white box testing. This testing method scans an application’s source code before compiling it to pinpoint areas susceptible to an attack. A SAST analysis takes place at the beginning of the software development lifecycle and helps identify security gaps before full deployment.
Conversely, the other methodology is Dynamic Application Security Testing (DAST). This technique involves scanning an already deployed web application to identify security flaws in real-time. In addition, the DAST method operates with an outside-looking-in approach where you conduct a penetration test to determine defects while the application runs. So it’s an ideal test for post-deployment.
On the other hand, the Static Application Security Testing (SAST) approach works best pre-deployment by identifying code injection and Cross-Site Scripting (XSS) vulnerabilities.
Vulnerability assessments or scans are typically conducted by third-party partners or your company’s IT security teams. These scans detect and classify defects by running specialized software within your computing devices, networks, servers, and backup systems.
The software compares the attack surface findings against a database containing known paths to potential attacks, flaws, bugs, default configurations, and other vulnerabilities commonly exploited by attackers.
Once the software completes the vulnerability assessment, it generates a report with findings to develop security remediation and mitigation solutions.
Vulnerability Assessment Tools
Vulnerability assessments are done through an automated process performed by sophisticated scanners to detect all forms of vulnerabilities. Additionally, vulnerability scanners classify according to how they operate and the technology layer they handle. They include:

Network-Based Vulnerability Scanning Tools
Network-based assessment tools search for vulnerabilities within a company’s private network by scanning IP addresses and open ports. These tools apply various techniques to identify flaws in communication channels and determine whether they can pass through the firewall.
Examples of techniques used with network scanning tools are:
- Ping sweeping – determines IP address ranges mapped to active devices.
- Transmission Control Protocol (TCP) connect – detects open ports once communication between a client and the server completes.
- Acknowledgement (ACK) flag probe scanning – identifies if ports are open or closed by sending ACK flags with TCP probe packets.
Host-Based Vulnerability Scanning Tools
Host-based assessment tools identify flaws and weaknesses in specific computing and network devices. For example, the scan focuses on a single server, router, workstation, or computer. The goal of such tools is to provide visibility into device configurations and security patch history. They perform individual scans on each device to identify specific vulnerabilities in each host.
Database Vulnerability Scanning Tools
Database vulnerability scanning tools identify security defects within your database management systems to prevent SQL injection attacks. The equipment also explores database configurations to identify potential vulnerabilities that attackers can exploit. Additionally, the database vulnerability scanner helps in meeting compliance standards that require database security assessment reports.
Cloud-Based Vulnerability Scanning Tools
Cloud-based assessment tools scan for security flaws in your cloud infrastructure. These scanners perform scans through predictive analytics powered by AI and machine learning. In addition, the scanners integrate with your enterprise software and business applications to deliver a holistic assessment report.
Vulnerability Assessment: Step-by-Step Guide
Below we highlight the network vulnerability assessment steps and the vulnerability assessment process flowchart. This guideline will help you streamline your vulnerability assessment procedures and implement remediation plans effectively. The typical vulnerability assessment processes include:
Step 1: Asset Inventory and Risk Assessment
The first stage involves identifying your IT assets and creating an accurate inventory for all devices. Next, assess the risk associated with each piece of equipment, potential vulnerabilities, risk tolerance levels, and mitigation solutions for each device. Additionally, you’ll need to identify the business impact for vulnerabilities identified in each device then develop countermeasures to prevent business or financial losses.
Proceed to document your findings once you have a conclusive inventory and risks associated with each device.
Step 2: System-Level Review and Prioritization
The second stage deals with identifying specific system configurations that expose the devices to potential attacks. This prioritization helps you in allocating security resources to critical attack surfaces before dealing with low-risk vulnerabilities.
Some areas you can prioritize in the assessment process are:
- Internet-facing systems and networks
- Customer-facing software and applications
- Databases
- Networks
Step 3: Run the Vulnerability Scanners
Proceed to identify suitable vulnerability scanners based on the information collected in stages one and two. Your vulnerability assessment service provider should guide your company on the most effective tool for the job. A typical vulnerability assessment platform does three things:
- Scanning open ports
- Probing software security patches and versions
- Scanning configuration settings
Once you establish that the software performs the basic scanning procedures, you can customize it to assess your systems based on the risk criteria you provide and the desired coverage.
Step 4: Assessment Results Analysis
At this stage, the scanning tool will generate a report with information about the vulnerability severity and level of exposure. With this information, organizations can develop remediation solutions to protect the company from potential attacks.
How Can I Tell if my Organization Requires a Vulnerability Assessment?
Every organization, regardless of how secure they think their systems are, critically needs consistent vulnerability assessments. Cybercriminals constantly scan for system weaknesses to exploit while malware evolves and becomes more sophisticated.
On the other hand, the sheer amount of potential vulnerabilities that companies face means you’ll handle security risks in one way or another. Therefore, the best practice is to proactively identify vulnerabilities and resolve them routinely while enhancing your security programs with more robust protection policies. CG Technologies can help you identify, remedy and monitor your IT environment for potential threats. Contact us to discuss how our range of managed security services can benefit your business.
